Article
Beyond Human Error: Understanding the Complete Security Chain in Information Security
Author: Agus Budi Harto, 2026-01-01 20:10:26
Introduction: Rethinking the "Weakest Link" Paradigm
In the realm of information security, we've all heard the age-old adage: "humans are the weakest link." While this statement holds undeniable truth, it presents an incomplete picture of the complex landscape of security vulnerabilities that organizations face today. The reality is far more nuanced and interconnected than a single point of failure might suggest.
This narrow focus on human error, though important, can create a dangerous blind spot in organizational security strategies. By viewing security through the lens of "the weakest link," we risk overlooking the intricate web of vulnerabilities that exist across every layer of our information systems. More critically, we fail to recognize that humans are not just one isolated link in the chain—they are embedded throughout every aspect of security infrastructure, from strategic decision-making to daily operational tasks.
The Security Chain: Understanding All the Links
When we conceptualize information security as a chain, it becomes clear that multiple interconnected components work together to protect organizational assets. Each of these "links" represents a critical domain that requires equal attention and fortification. Understanding this complete security chain is essential for building a resilient defense posture.
1. The Technology and Technical Link
The technological foundation of any security infrastructure encompasses hardware, software, operating systems, and security tools. This link includes servers, endpoints, network devices, firewalls, intrusion detection systems, and antivirus solutions. Each component carries its own set of vulnerabilities, from unpatched software and zero-day exploits to configuration errors and architectural weaknesses.
Modern technology stacks have become increasingly complex, with cloud services, containerization, and microservices architectures adding new layers of potential vulnerability. The rapid pace of technological change means that what was secure yesterday may be vulnerable today, requiring constant vigilance and adaptation.
2. The Process Link
Organizational processes form the procedural backbone of security operations. This encompasses security policies, change management workflows, incident response procedures, backup and recovery protocols, and access control processes. When processes are poorly designed, inconsistently applied, or inadequately documented, they create exploitable gaps in security defenses.
The process link often represents the bridge between technical capabilities and organizational objectives. Even the most sophisticated security technologies become ineffective without robust processes to govern their use, maintenance, and continuous improvement.
3. The Physical Link
Physical security remains a critical yet sometimes overlooked component of information security. This includes building security, data center protections, environmental controls, physical access systems, and secure hardware disposal procedures. A breach of physical security can bypass even the most sophisticated digital defenses, providing attackers with direct access to critical infrastructure.
4. The Network Link
Network architecture, communication channels, wireless networks, internet connectivity, and remote access solutions comprise the network link. This domain has expanded dramatically with the rise of remote work, bring-your-own-device policies, and the proliferation of Internet of Things devices, each introducing new attack vectors and security challenges.
5. The Data Link
At the heart of information security lies the data itself. Data storage systems, databases, transmission mechanisms, backup systems, and archival processes all represent potential points of vulnerability. The value of data makes it a prime target, and inadequate protection at any stage of the data lifecycle can result in catastrophic breaches.
6. The Organizational and Management Link
Strategic leadership, governance structures, budget allocation, and risk management constitute the organizational link. Executive decisions about security investments, risk appetite, and organizational priorities directly impact the strength of all other security links. Without proper support and resources from leadership, even the best technical and operational security measures will fall short.
7. The Third-Party and Supply Chain Link
In today's interconnected business environment, organizations depend heavily on vendors, suppliers, cloud service providers, outsourced services, and business partners. Each of these relationships introduces additional risk, as a vulnerability in a partner's systems can become a backdoor into your own infrastructure. Supply chain attacks have emerged as one of the most challenging security threats of the modern era.
8. The Compliance and Legal Link
Regulatory requirements, legal obligations, industry standards, contractual agreements, and audit requirements form the compliance link. Non-compliance not only carries legal and financial penalties but can also indicate underlying security weaknesses that attackers might exploit.
The Comprehensive Vulnerability Landscape
Understanding the security chain helps us recognize that vulnerabilities exist across multiple dimensions, each requiring specific attention and mitigation strategies.
Technical and Technological Vulnerabilities
Software bugs, coding errors, and zero-day vulnerabilities represent ongoing challenges in the technical domain. Unpatched systems and outdated software create well-documented attack paths that malicious actors routinely exploit. Weak authentication mechanisms, insufficient encryption, poor cryptographic implementation, and default configurations provide easy entry points for attackers.
The technical vulnerability landscape also includes SQL injection flaws, buffer overflows, cross-site scripting vulnerabilities, and numerous other programming errors that can compromise system integrity. These vulnerabilities often stem from rushed development timelines, inadequate security testing, or insufficient security awareness among developers.
Architecture and Design Vulnerabilities
System architecture vulnerabilities arise from fundamental design flaws rather than implementation errors. Single points of failure, insufficient network segmentation, lack of defense in depth, and poor system architecture create structural weaknesses that can be difficult and expensive to remediate after deployment.
Inadequate redundancy, weak access control design, and improper trust boundaries represent architectural decisions that can have lasting security implications. These vulnerabilities highlight the critical importance of incorporating security considerations from the earliest stages of system design.
Configuration Vulnerabilities
Even perfectly designed and coded systems can be rendered vulnerable through misconfiguration. Misconfigured firewalls and security devices, unnecessary services running on production systems, excessive user privileges, weak password policies, and unnecessary open ports represent some of the most common and easily exploitable vulnerabilities in modern systems.
Configuration vulnerabilities are particularly insidious because they often result from well-intentioned but misinformed decisions, lack of expertise, or simple oversight during system deployment and maintenance.
Process and Procedural Vulnerabilities
Inadequate change management, poor patch management processes, weak incident response procedures, insufficient logging and monitoring, and lack of regular security testing all represent procedural vulnerabilities. These weaknesses in organizational processes can undermine even the strongest technical controls.
Poor backup procedures, inadequate vendor management, and lack of documented security procedures mean that organizations may be unable to respond effectively when security incidents occur, turning manageable situations into full-blown crises.
Physical Vulnerabilities
Inadequate physical access controls, poor environmental controls for temperature and humidity, lack of surveillance, unprotected cables and networking equipment, and poor disposal procedures for hardware all contribute to physical vulnerabilities. These often-overlooked weaknesses can provide attackers with opportunities to bypass digital security measures entirely.
Communication Vulnerabilities
Unencrypted data transmission, use of insecure protocols like HTTP, FTP, or Telnet, weak wireless security, and susceptibility to man-in-the-middle attacks represent communication vulnerabilities. DNS vulnerabilities and improper certificate management can also enable various forms of attack and data interception.
Organizational Vulnerabilities
Lack of comprehensive security policies, insufficient security budgets, poor risk assessment practices, inadequate business continuity planning, and weak third-party management represent organizational-level vulnerabilities. These systemic weaknesses often enable or exacerbate vulnerabilities at other levels of the security chain.
Insufficient security awareness programs fail to prepare employees to recognize and respond appropriately to security threats, creating human vulnerabilities that attackers can exploit through social engineering and other tactics.
Data Vulnerabilities
Insufficient data classification means organizations may not know which data assets require the strongest protection. Poor data retention policies, inadequate data backup, lack of data integrity controls, and improper data disposal can all lead to data loss, corruption, or unauthorized access.
Where Humans Fit in the Vulnerability Landscape
Here lies the critical insight that transforms our understanding of human factors in security: humans are not merely one isolated link in the security chain. Rather, humans are embedded throughout every category of vulnerability, influencing, creating, and potentially mitigating security risks at every level.
Humans in Technical Vulnerabilities
Developers write code that contains bugs and vulnerabilities. System administrators forget to apply critical patches or fail to follow through on scheduled maintenance. IT staff incorrectly implement encryption protocols or cryptographic systems. Engineers use default passwords in production environments. Programmers inadvertently introduce SQL injection vulnerabilities through inadequate input validation.
Each technical vulnerability, when traced back to its origin, typically reveals human decisions, actions, or oversights. The technology itself is neutral; it's the human interaction with that technology that introduces weakness.
Humans in Architectural Vulnerabilities
Architects design systems with single points of failure due to budget constraints, incomplete requirements, or insufficient consideration of failure scenarios. Network engineers fail to implement proper segmentation, either through lack of knowledge or organizational pressure to prioritize convenience over security. Security designers neglect to implement defense in depth, perhaps underestimating potential threats or overestimating the strength of perimeter defenses.
IT managers make decisions about redundancy based on incomplete risk assessments or budgetary pressures, potentially leaving critical systems vulnerable to outages or attacks.
Humans in Configuration Vulnerabilities
System administrators misconfigure firewalls, either through lack of training, inadequate documentation, or simple human error. IT staff allow unnecessary services to run on production systems, perhaps not fully understanding the attack surface they create. Administrators grant excessive privileges to users or service accounts, often in response to urgent business needs without properly considering security implications.
Security officers implement weak password policies, potentially balancing usability concerns against security requirements without fully understanding the risks. Network administrators leave unnecessary ports open, perhaps as temporary measures that become permanent through oversight or lack of formal change control.
Humans in Process Vulnerabilities
Change managers bypass or inadequately follow change management procedures, often under pressure to deliver quickly or resolve urgent issues. IT teams ignore patch management schedules due to fear of system instability or business disruption. Security teams fail to develop adequate incident response plans, perhaps underestimating the likelihood of security incidents or lacking the resources to plan comprehensively.
Auditors neglect to conduct regular security testing, possibly due to resource constraints or lack of organizational priority. Backup operators fail to verify backup integrity or monitor backup procedures, creating situations where organizations discover their backups are unusable only when disaster strikes.
Humans in Physical Vulnerabilities
Security guards inadequately monitor physical access, whether through complacency, inadequate training, or understaffing. Facilities managers neglect environmental controls, perhaps not fully understanding their role in protecting information assets. Staff members fail to secure server rooms, either through oversight or lack of awareness about physical security importance.
Employees dispose of hardware improperly, not understanding that deleted data can often be recovered from improperly disposed devices, or simply taking shortcuts in disposal procedures.
Humans in Communication Vulnerabilities
Network administrators fail to encrypt data transmissions, perhaps prioritizing performance over security or lacking the knowledge to implement encryption properly. IT staff continue using insecure protocols like HTTP, FTP, or Telnet, often because legacy systems require them and no one has prioritized migrating to secure alternatives.
Users connect to wireless networks without proper security measures, either unaware of the risks or prioritizing convenience. Administrators misconfigure DNS systems or fail to implement DNSSEC, potentially enabling various forms of attack.
Humans in Organizational Vulnerabilities
Management fails to create comprehensive security policies, perhaps viewing security as an IT problem rather than an organizational imperative. Executives allocate insufficient security budgets, potentially not understanding the true cost of security breaches or prioritizing other business objectives.
Risk managers conduct inadequate risk assessments, possibly lacking the tools, knowledge, or organizational support needed for comprehensive analysis. HR departments fail to implement effective security awareness programs, treating security training as a compliance checkbox rather than a critical business function.
Procurement teams inadequately vet vendors and third parties, perhaps prioritizing cost and speed over security considerations in vendor selection.
Humans in Data Vulnerabilities
Data owners neglect data classification, perhaps overwhelmed by the volume of data or lacking clear guidelines. Records managers fail to establish appropriate retention policies, either through oversight or inadequate understanding of regulatory and business requirements.
Backup administrators don't verify backup integrity, potentially discovering only during recovery attempts that backups are corrupt or incomplete. Staff members improperly dispose of data, either through ignorance of proper procedures or lack of available resources for secure disposal.
Database administrators fail to implement adequate data integrity controls, potentially through incomplete understanding of threats or insufficient time allocated to security hardening.
Case Study: PT Pamapersada Nusantara's Identity and Access Management Improvement
A compelling real-world example illustrates how multiple vulnerabilities can converge in a single security scenario and how addressing them requires a comprehensive approach. PT Pamapersada Nusantara, a major mining services company, identified and remediated a significant security vulnerability in their identity and access management processes.
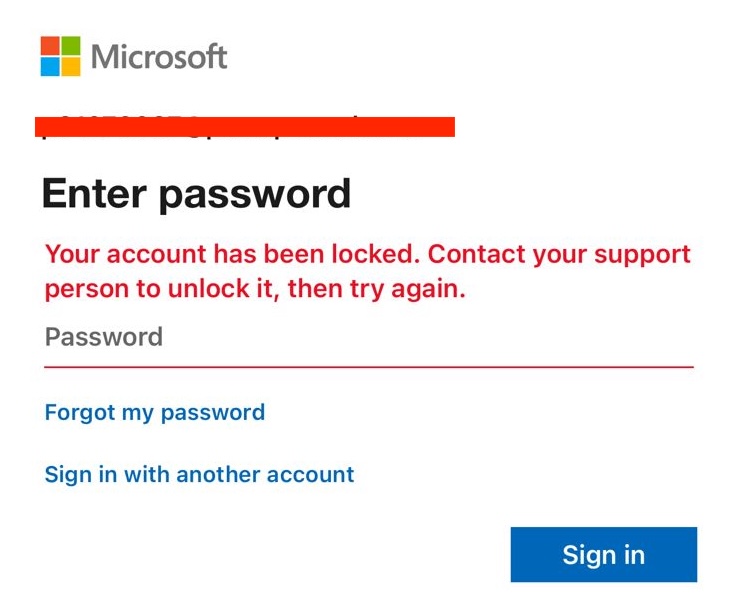
The Vulnerability: Pre-Remediation State
Before implementing improvements, PT Pamapersada faced a situation where employees who had retired still retained active domain access credentials. This meant that former employees could potentially log into company systems days, weeks, or even months after their employment had ended. This vulnerability exemplified several categories of security weakness simultaneously.
Analysis of Contributing Vulnerabilities
Technical and Configuration Vulnerabilities: The company's access control mechanisms lacked automated deprovisioning capabilities. The Identity and Access Management system was not configured to automatically disable accounts based on employment status changes. This created "orphaned accounts"—user credentials that remained active despite no longer being associated with current employees.
Process and Procedural Vulnerabilities: The organization suffered from inadequate user lifecycle management processes. There was no automated workflow connecting HR employment status changes with IT access management actions. The offboarding process for "leavers" in the joiners-movers-leavers framework was either non-existent or ineffectively implemented. Access review procedures were insufficient, meaning that dormant accounts were not identified and disabled through periodic review.
Organizational Vulnerabilities: A critical gap existed between HR systems and IT security systems, with no integration or automated data flow between these domains. The lack of coordination between departments meant that when HR processed a retirement, this information did not automatically trigger access revocation in IT systems. Access governance policies were either unclear or not consistently enforced.
Human Elements Throughout: The vulnerability involved humans at multiple points. HR staff processed retirements without a clear mechanism to notify IT. IT administrators lacked automated systems to remove access and relied on manual processes that could be overlooked. Managers may have failed to notify IT of departing team members. Former employees retained access through no malicious intent of their own, but simply because the system didn't remove it.
The Solution: Implementing Comprehensive Controls
PT Pamapersada's remediation demonstrates security best practices in action. They implemented an automated account deactivation system that responds immediately to employment status changes. Integration between HR systems and Active Directory or their IAM platform ensures that when an employee's status changes to "retired" or "terminated," this triggers immediate action in access management systems.
The company now achieves real-time or near real-time access revocation, with the case study noting that employees cannot log in to domain systems even one day after retirement. This represents a robust offboarding process that eliminates the window of opportunity for unauthorized access by former employees.
The Broader Implications
This case study illustrates several critical principles of information security:
Multiple Vulnerabilities Converge: What appeared as a single issue—former employees retaining access—actually represented the intersection of technical, procedural, and organizational vulnerabilities. Addressing it effectively required interventions at all these levels.
Human Factors Permeate the Scenario: While the solution involved technical automation, the original vulnerability stemmed from human factors: process design decisions, resource allocation choices, and the coordination (or lack thereof) between different organizational functions.
Holistic Approaches Are Essential: The fix required not just technical implementation but also process redesign, cross-departmental coordination, and ongoing governance to ensure the solution continues to function as intended.
Prevention Is Superior to Detection: Rather than relying on periodic access reviews to eventually discover and remove orphaned accounts, the automated approach prevents the vulnerability from existing in the first place.
The True Nature of "Human as the Weakest Link"
With this comprehensive understanding of the security landscape and where humans fit within it, we can now properly contextualize the statement that "humans are the weakest link."
Humans Are Not One Link—They Are Embedded in Every Link
The fundamental insight is that humans don't represent a single, isolated point of failure in the security chain. Instead, humans are embedded throughout every component of information security infrastructure:
Decision Makers: Executives and managers make strategic decisions about security investments, risk tolerance, and organizational priorities. These decisions shape the entire security posture of the organization.
Implementers: IT professionals, developers, system administrators, and security specialists implement technical controls, configure systems, and build the actual security infrastructure.
Operators: Daily users, employees across all functions, and operational staff interact with systems, handle data, and execute processes that either strengthen or weaken security.
Third Parties: Vendors, contractors, and partners bring their own human factors into the security equation, extending the human element beyond organizational boundaries.
Why Humans Remain the "Weakest Link"
Humans are considered the weakest link not because they constitute a single point of failure, but because:
Ubiquitous Presence: Humans are involved at every decision point, control mechanism, and operational task within the security chain. This ubiquity means that human factors influence security outcomes at every level.
Complexity of Human Behavior: Unlike technology, which behaves predictably according to its programming, humans are subject to cognitive biases, emotional states, fatigue, distraction, and myriad other factors that affect their decision-making and behavior.
Susceptibility to Manipulation: Humans can be deceived through social engineering, phishing, pretexting, and other manipulation techniques. No amount of technical security can fully protect against a user who has been convinced to hand over their credentials or install malware.
Potential for Error: Human error represents a constant risk factor. Even well-trained, security-conscious individuals can make mistakes, especially when facing time pressure, ambiguous situations, or conflicting priorities.
Access to Systems: Humans possess legitimate access to systems, data, and processes. This necessary access means that humans can, whether through malice or mistake, cause security breaches from within the organization's security perimeter.
Variation in Capability: Unlike standardized technical systems, humans vary enormously in their knowledge, skills, awareness, and commitment to security practices. This variation creates inconsistencies in security posture across the organization.
The Paradox: Humans as Both Weakness and Strength
While humans introduce vulnerabilities throughout the security chain, they also represent the ultimate defense. Humans can:
- Detect anomalies that automated systems miss
- Apply contextual judgment to ambiguous situations
- Adapt to new and evolving threats
- Design and implement security innovations
- Make ethical decisions in complex scenarios
- Provide the oversight and governance that ensures security programs remain effective
This paradox means that effective security strategies must simultaneously acknowledge human vulnerabilities while leveraging human capabilities.
Building a Holistic Security Strategy
Understanding the complete security chain and the pervasive role of human factors should fundamentally reshape how organizations approach information security.
Move Beyond Single-Point Solutions
Security strategies must address all links in the security chain simultaneously. Investing heavily in technical controls while neglecting process improvements or organizational governance creates exploitable gaps. Similarly, focusing exclusively on user awareness training while allowing technical vulnerabilities to persist leaves the organization exposed.
Implement Defense in Depth
The principle of defense in depth assumes that any single security control might fail. By implementing multiple layers of security controls across different domains—technical, physical, administrative—organizations ensure that a failure in one area doesn't result in a complete security breach.
Embrace the Socio-Technical Perspective
Modern security thinking recognizes that information security is fundamentally a socio-technical challenge. Technology and humans interact in complex ways, and effective security requires understanding and addressing this interaction, not treating them as separate domains.
Invest in Security Culture
Since humans are embedded throughout the security chain, organizational culture becomes a critical security control. A strong security culture means that security considerations are naturally incorporated into decision-making at all levels, reducing the likelihood of security-impacting errors or oversights.
Continuous Assessment and Improvement
The threat landscape, technology environment, and organizational context all change continuously. Security strategies must include mechanisms for continuous assessment of vulnerabilities across all domains and continuous improvement of controls and processes.
Integration and Automation
As demonstrated by the PT Pamapersada case study, integrating systems and automating security processes can dramatically reduce vulnerabilities that stem from manual processes and human oversight. However, automation must be thoughtfully designed and regularly reviewed to ensure it functions as intended.
Conclusion: Toward Comprehensive Security Understanding
The statement "humans are the weakest link" contains truth, but it's an incomplete truth that can mislead security thinking if not properly understood. Humans are not a single weak link in an otherwise strong chain. Rather, humans are woven throughout the entire security fabric, influencing every aspect of information security from strategic decisions to daily operational tasks.
True security maturity comes from recognizing that vulnerabilities exist across multiple dimensions—technical, architectural, configurational, procedural, physical, communicational, organizational, and data-related. Humans play critical roles in each of these dimensions, both as potential sources of vulnerability and as essential elements of security defense.
Organizations that achieve strong security postures do so by taking a holistic approach that addresses all links in the security chain while specifically acknowledging the pervasive human element. They implement technical controls while also improving processes, they automate where appropriate while maintaining necessary human oversight, and they invest in user awareness while also addressing architectural and organizational vulnerabilities.
The goal is not to eliminate humans from the security equation—that would be neither possible nor desirable. Instead, the goal is to design systems, processes, and organizational structures that account for human factors, that leverage human strengths while mitigating human weaknesses, and that create security postures resilient enough to withstand the inevitable failures that will occur in any complex system.
By moving beyond the simple narrative of "human as the weakest link" to embrace a more comprehensive understanding of the security chain and the role of humans within it, organizations can build more robust, resilient, and effective information security programs that protect their assets, data, and reputation in an increasingly complex and threatening digital landscape.
The path forward requires acknowledging complexity rather than seeking simple answers, investing across all dimensions of security rather than focusing on isolated areas, and recognizing that effective information security is ultimately a human endeavor requiring human wisdom, judgment, and continuous commitment to improvement.
Tags: Expression Mining Opinion
Add comment
- Other Article
- Organisasi Pensiunan di Indonesia: Dari Komunitas Sosial Menuju Kekuatan Ekonomi Berbasis Pengalaman12 May 2026
- Corporate Risk Management: Why Modern Companies Invest Millions to Prevent Invisible Threats07 May 2026
- The Mining Spirit: A Powerful Mindset for Excellence in the Mining Industry25 Apr 2026
- The Double-Edged Sword: Navigating Competition in the Modern Corporate Landscape22 Apr 2026
- AI Chatbot untuk UMKM: Peluang Besar di Era Digital17 Apr 2026
- AI Chatbots in Business: The Global Revolution09 Apr 2026
- The Heartbeat of Your Business: Why the P&L Statement is Non-Negotiable31 Mar 2026
- Why Your New Business Needs a Financial System on Day One26 Mar 2026
- The Link Between Startup Capital, Business Survival, and the Role of Investor Information21 Mar 2026
- Digital Transformation, Digitalization, and Digitization: Why the Difference Matters More Than You Think14 Mar 2026
- From Business Need to Technology Solution07 Mar 2026
- Bridging the Digital Divide: Starlink and the Future of Internet Access in Indonesia27 Feb 2026
- A Long Weekend Getaway to Yogyakarta16 Feb 2026
- Understanding ERP Systems: A Comprehensive Guide for Modern Businesses16 Feb 2026
- Building a Culture of Awareness: Strategic Approaches to HSE and Information Security Campaigns in Modern Organizations10 Feb 2026
- Building an Effective IT Organization in Coal Mining: A Strategic Framework for Growth02 Feb 2026
- The Art and Science of Color Themes in Modern Web Design17 Jan 2026
- IT Outsourcing vs Internal Resources: A Comprehensive Cost and Risk Analysis05 Jan 2026
- The Hidden Dangers of Mishandled Employee Data: When Internal Tables Fall Into the Wrong Hands05 Jan 2026
- Securing SQL Server: A Complete Guide to Database Access Control05 Jan 2026
- Beyond Human Error: Understanding the Complete Security Chain in Information Security01 Jan 2026